Email is the gateway used by most hackers to launch their nefarious schemes. Today’s hackers are far more sophisticated than before, and they’re willing to take their time to gather the information they need to successfully hack into your organization. Your best phish defense – besides layers of security and a great MSP partner – is employee education. Training your staff on what to look for in a phishing email and to be cautious with every email – even those that look like they come from your CEO – could potentially save your organization hundreds of thousands of dollars.
The First Danger of a Phishing Email: Know Who It’s From
Be honest: If you were busy and you received an email from john@qutterinstallers.com, would you really notice that the email address was off by one letter? Now go back and look at the email address. You probably thought it read ‘john at Gutterinstallers.com,’ right? But in reality, it read ‘john at Qutterinstallers.com.’ Yes, hackers are that subtle. Because not only can they make emails look like they have been sent from an internal address, but they can also insert themselves mid-conversation into an email thread so that you really do think you’re talking to the right person. This is why every email requires the same vigilance – even if you think it’s from your boss or best client.
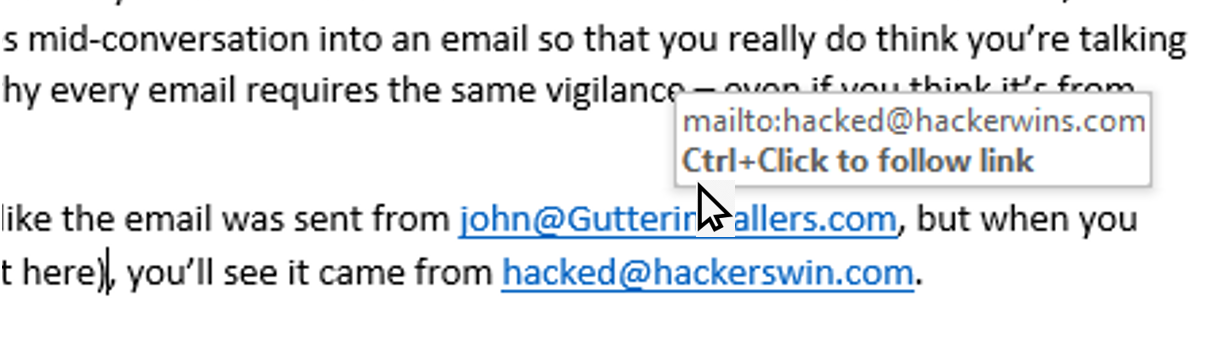
Hackers can also make it look as if an email was sent from john@Gutterinstallers.com, but when you hover over the email link (try it here), you’ll see that, in fact, it was sent from hacked@hackerswin.com.
Keep these questions in mind with every email you receive:
- Is the sender unfamiliar to you?
- When you hover over the email address, is it different than what appears in the header?
- Is the email out of character?
- Is the email from someone outside of your organization and asking you to do something outside of your typical role?
- Is the sender a stranger?
- Does the email include a link or attachment?
No Action without Asking
It should be the policy of every company not to pay invoices, click links, open attachments, or take other actions without at least asking if it’s possible that the email could be fake. Look for these telltale clues and red flags in an email header:
- Did the email arrive at an odd hour?
- Is it from someone you don’t know or addressed differently than you would expect?
- Is your name spelled incorrectly?
- Is the email sent to multiple people, making the same request?
When you’re always on high alert about the potential risks of email, you’ll start noticing when something seems off. Watch for these clues:
- Is it asking you to do something that’s not really your job?
- Is there a sense of urgency or threat from the email that attempts to emotionally compromise you into taking action?
Don’t Click
If there is a link in an email, you should be on high alert. You can often tell when it’s a phishing email. Try these steps: When you hover over (but don’t click) on the link, does it go to a different website than what it says in the text? Does the hyperlink look similar to a legitimate website but differ, if only slightly?
Don’t Open
Does the email contain an attachment? Is the attachment a file of any type other than a text file (.txt)? Were you expecting the attachment because of a previous conversation or is it out of the blue? Does the message seem to pressure you into taking action of some kind?
Protect Your Organization Against Phishing Attacks
Strong spam filtering can stop most phishing emails, but some will still make it through. At this point, your employees are your final line of defence against an attack. Yes, your firewall and threat management software should protect you, but without extensive training and awareness, a plan of action to protect your data, and non-stop vigilance, email may be what brings your organization down.
Download The ITeam’s Email Security Guide
Your greatest weakness can also be your greatest strength if you invest the necessary time and resources in educating your employees. When education is provided, employees become a partner in your overall cybersecurity efforts. The ITeam understands the email security issues facing Canada businesses. We are committed to helping Calgary- and Alberta-based businesses develop proactive, cost-effective IT strategies that minimize risk and maximize efficiency. Contact us to learn more.

